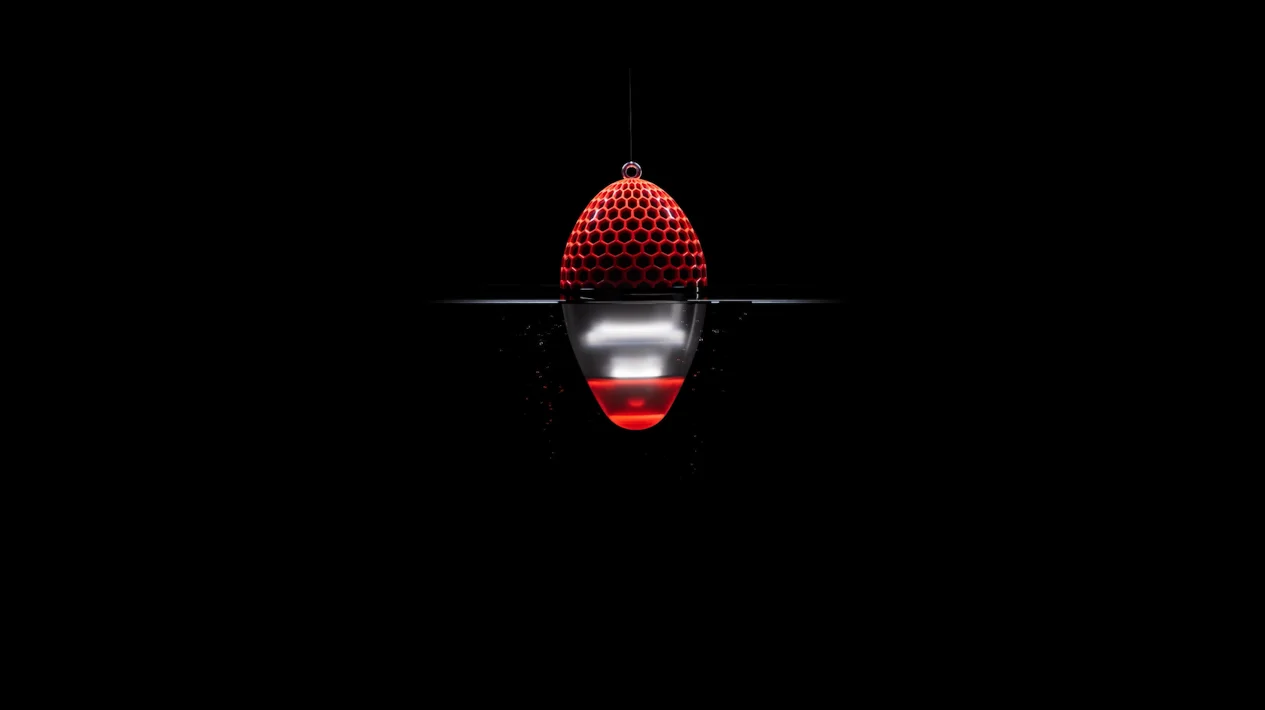
Light up your external attack surface
Lantern continuously inventories your external surface and highlights weaknesses that could lead to compromise.
Know before they do
Rapidity and exhaustivity are key.
Lantern helps you build a real-time inventory of your exposed services and continuously monitor the attack surface so you can close the doors before they’re tested.
What makes us different
The eASM space is growing fast, with many solutions available.
With Lantern, we chose to focus on two key differentiators that reflect how we believe external exposure should be managed.
Fully Granular Inventory
Inventory is crucial in cybersecurity. Our capabilities are granular, usable, and exhaustive, ensuring nothing is missing that could lead to breaches.
Unmatched Detection Speed
When it comes to exposed services, every minute counts, and nothing should be left to chance. Our solution is the fastest, helping you discover exposures before attackers strike.
Controlled discovery
Discover potential exposure the same way attackers do, without the noise of blind automation. Our discovery engine scans the Internet daily to flag assets that might belong to you, based on how they appear externally. You stay in control, nothing enters your inventory without your confirmation.
Instant cloud visibility
Identify and track every cloud asset you expose, using direct connectors with your cloud providers. Public IPs are added to your inventory in real time, so nothing slips through when new services spin up. Gain full visibility over dynamic exposure, without relying on guesswork or passive discovery.
Persistent knowledge
Document everything down to every exposed or even closed service, with full labeling and tracking, ensuring nothing is lost, overlooked, or forgotten. Build a living, structured inventory of your internet-facing assets, designed for operational clarity and long-term accountability.
Actual real-time detection
Lantern detects newly exposed services in under 30 minutes, not in hours or days. Most tools claim real-time detection, but in practice, they take 24 hours or more to react. We built Lantern to close that gap and give you the speed attackers won’t wait for.
Breach-oriented alerts
Lantern only alerts you for the most relevant exposures, the ones that attackers actually use to get in. We don’t flood you with irrelevant CVEs or low-impact findings. You stay focused on what really matters: real risks, not theoretical ones.
Deep exposure mapping
Lantern scans all 65,535 ports across your external perimeter to surface any exposed service, not just the usual suspects. Whether it runs on 443, 8443, or 41365, if it's listening, we find it. No blind spots. No assumptions. Just full coverage.
A clear path to a controlled perimeter
Build your exhaustive inventory
We combine your internal inventory data with our autodiscovery engine and cloud connectors to build a complete and accurate view of your external attack surface, so you know exactly what needs to be protected.
Reach a Clean State
Once your perimeter is
fully mapped, Lantern
scans every asset to
identify what shouldn’t
be exposed:
misconfigurations, risky
services, forgotten
systems. The goal: a
clean and secured
baseline that attackers
can’t use against you.
Monitor Any
Deviation
Once your perimeter is
clean, every new
exposure stands out.
Lantern continuously
monitors your external
surface to detect
anything that wasn’t
part of the secured
baseline. When
everything is under
control, anything new
deserves your full
attention.
What is Lantern, exactly?
Lantern is an External Attack Surface Management (EASM) solution designed to help you regain control over your external perimeter. It builds a complete, actionable inventory of your exposed assets and detects dangerous exposures in real time, before attackers can exploit them.
How is Lantern different from traditional EASM or ASM tools?
Most tools on the market promise “full visibility” through fully automatic scans. But automation alone often leads to noisy results, false positives, or even monitored assets that don’t belong to you.
Lantern takes a hybrid approach: it emulates attacker behavior to discover your assets, and lets you confirm or discard them with ease. This keeps your inventory accurate and trustworthy.
What kind of exposures can Lantern detect?
Lantern focuses on what really matters to attackers and defenders:
- Public-facing admin interfaces
- Weak or default credentials
- Vulnerable services or ports
- Misconfigured cloud assets
- Internet-facing shadow IT
- CVEs with confirmed exploitation paths
All findings are validated, prioritized, and ready to act on.
How fast does Lantern detect exposures?
Very fast.
Most critical services (like admin interfaces or remote access ports) are detected in under 30 minutes, not 24h+ like many traditional scanners. And that speed matters: an exposed RDP can be brute-forced within the hour. With Lantern, you can catch it before attackers do.
How does Lantern work with my cloud environments?
Lantern offers native connectors for major cloud providers (AWS, Azure, GCP) that pull your public-facing assets in real time. No manual exports, no delay. Your cloud footprint is always up to date.
This helps you avoid surprises when a misconfigured service goes live… without anyone knowing.
Will I be overwhelmed with alerts?
Not with Lantern.
The platform is built with prioritization in mind:
- You only receive alerts for exposures that are truly risky and exploitable.
- No endless lists of low-priority issues.
- No alerts for assets that aren’t yours.
Our team has a SOC background, so we’ve designed Lantern to report only what your team needs to act on, nothing more.
Do I need to install anything?
No installation required.
Lantern is a fully SaaS-based solution. You simply onboard, connect your cloud providers, review the suggested inventory, and let Lantern do the rest. Deployment takes minutes, not days.
Can Lantern integrate with our existing tools?
Yes.
Lantern can integrate with your SIEM, ticketing system, or SOAR platform, allowing you to automatically ingest relevant alerts and take action through your existing workflows.